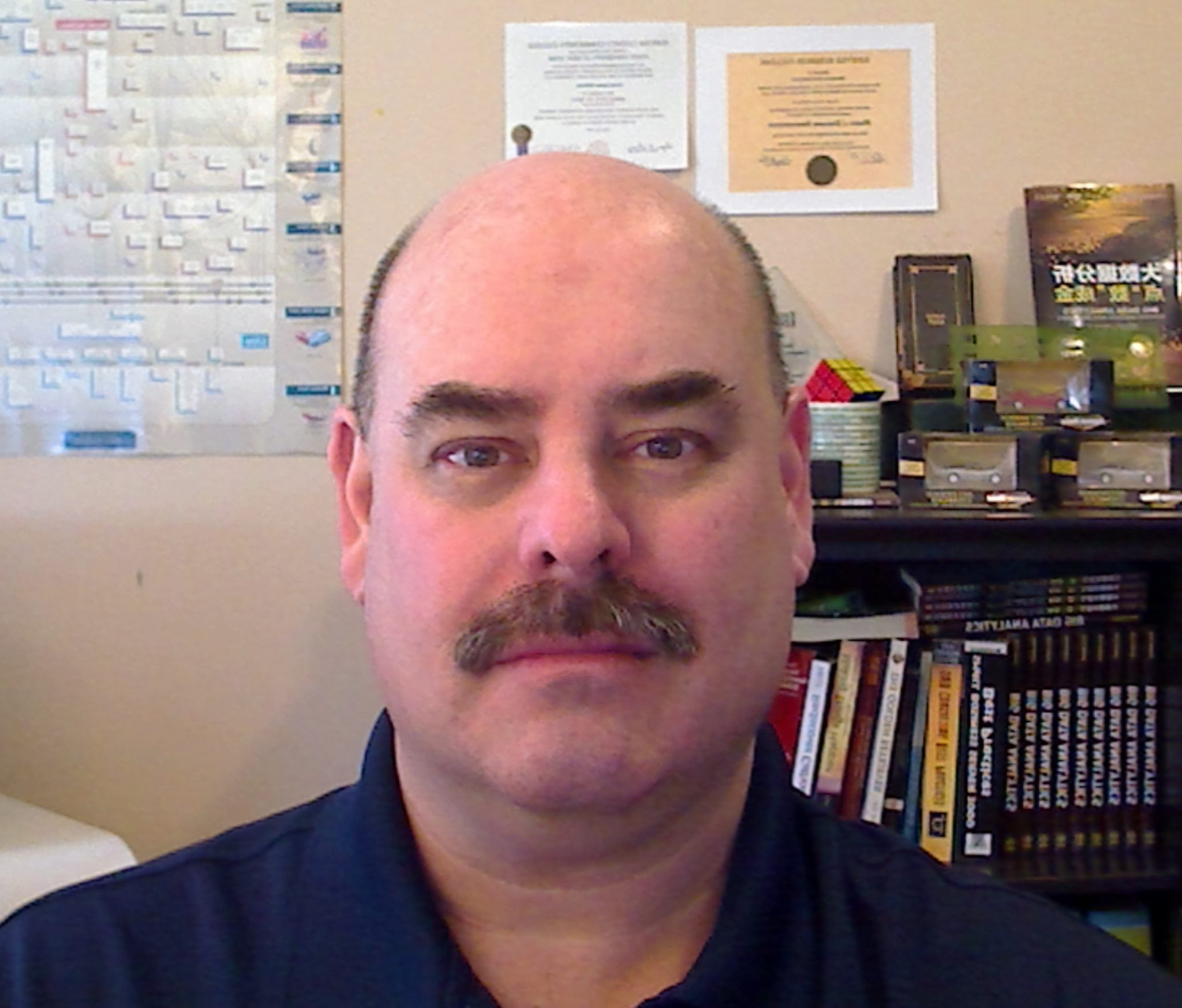
Abhijit Chatterjee is a world renowned personality in IT industry, a global top IT professional award winner, worldwide topper in MCP and certified IT specialist in various domains. Due to his expert IT consultation and advice, he has been recently selected and invited by Mauritius government to work with Prime Minister Office in Mauritius.
Abhijit Chatterjee is an Industry Certified Professional specialized in IT Infrastructure Management, Network Optimization, Cloud Implementation, Cyber Security, Consultation and Advisory, etc. Learning while earning concept and keeping up-to-date on new technologies made him “worldwide topper” (scored 1000 out of 1000) in MCP. His dedication towards constant learning on latest technologies made him Double MCP. His certification includes SBS Specialist, Certified Surveillance Consultant, Network Consultant, Security Specialist, Microsoft Pre-sales Technical Expert, IBM Storage & Server Sales Specialist, and so on. His consultations and implementations have significantly reduced IT Processes, Manpower, CapEx and OpEx to various Central Government Departments, State Governments, Universities, Banks, Public Sector and Private Sector companies, SMEs, SOHOs and MNCs. He has working knowledge of more than 20 years.
Mr. Chatterjee is highly motivated, organized and detail-directed problem solver. He is very efficient in managing IT Operations, Infrastructure Services, IT Procurement, Vendor Management, Optimization of IT Budget and Resource Utilization. Management of Storage, Server and Virtualization, Deployment of Software and Network, Implementation of Cloud and Cyber Security are some of his forte.
He has a strong technical background and knowledge in multiple domains in IT. He is an effective leader with distinguished abilities in project implementation and motivating team members to maintain deliverables as per SLAs. He has proven ability to perform in stress and scarce resource conditions.
He was the winner of India’s Top-100 ICT Projects Award 2012, ChannelWorld Premier100 Award 2015, 2016, 2018 and 2019, Most Influential CIO/CTOs of India Award 2015, Business Technology Award 2015 on IoT, SME Channels Award for the three consecutive years -Super50 Awards in 2016, Super100 Awards in 2017 and Infrastructure Specialist Awards in 2018, YES BANK’s Most Promising Future CFOs of India 2016, Dataquest Vertical Warrior Award 2016 in IT/ITeS, IDG Insights Award in Technology for two times – Excellence in Innovation in 2015 and Excellence in Operations in 2017, 4th Datacenter Award 2018, 5th Datacenter Award 2018, Great Indian Workplace Awards 2018, IT Security Awards 2018, Business Leader of the year Award 2018, Innovation and Technology Leader of the year Award 2018. This year (in 2019) till June end, he won six awards in IT and that continues…
Today, he is known by his work, achievements, awards and recognitions. He is not only known in India but also in International community. At every stage, he makes India proud. We are proud to say “He is a global personality in IT world and a gem of India”.
How do you interact with Microsoft 365?
In India, we sell and support Microsoft products including Office 365, Exchange, Azure, etc. We interact through email with Microsoft 365.
Tell us one customer story about Microsoft 365.
One of our client placed an order for cloud implementation. We quoted in two parts – Sales Quote, and, Service Quote. When they asked why we quoted 10% higher service charges, we informed this 10% goes to back to community and society. And that was our 1st customer who agreed. Since then we charged 10% extra and contribute the same to community.
How do you give back to your community?
We contribute in the form of serving meals to families who can’t afford 3 times meals, feeding roadside animals, help medicines for senior citizens, monetory help to fellow Indian citizens and below poverty line families, books and study materials to under privileged students, volunteer at local school for computer classes and training, tutor local students,
and so on.